Security in cloud computing is a crucial concern. Data in cloud should be keep in encrypted form. To restrict client from obtain the shared data directly, attorney and brokerage services should be employed.
Security Planning
Before deploying a specific resource to cloud, one should need to analyze several feature of the resource such as:
- Select resource that needs to move to the cloud and examine its sensitivity to risk.
- Review cloud service models such as IaaS, PaaS, and SaaS. These models demands customer to be responsible for security at different levels of service.
- Scrutinize the cloud type to be used such as public, private, community or hybrid.
- Understand the cloud service provider’s system about data storage and its pass on into and out of the cloud.
The risk in cloud lineup mainly depends upon the service models and cloud types.
Understanding Security of Cloud
Security Boundaries
A precise service model defines the boundary linking the responsibilities of service provider and customer. Cloud Security Alliance (CSA) stack model describes the boundaries between each service model and shows how different functional units relate to each other. The below diagram shows the CSA stack model:
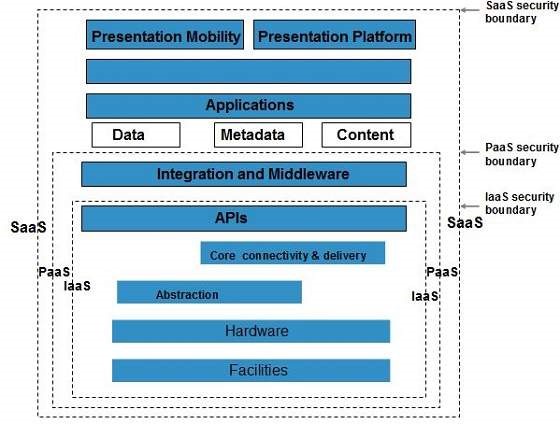
Major Points to CSA Model
- IaaS is the prime basic level of service with PaaS and SaaS next two high levels of services.
- Moving upwards, each of the service inherits potential and security concerns of the model beneath.
- IaaS give the infrastructure, PaaS provides platform development environment, and SaaS provides operating environment.
- IaaS has the least level of consolidate functionalities and integrated security while SaaS has the most.
- This model describes the security boarders at which cloud service provider’s responsibilities end and the customer’s responsibilities begin.
- Any security contrivance below the security boundary must be built into the system and should be maintained by the customer.
Although each service model has security contrivance, the security needs also depend upon where these services are located, in private, public, hybrid or community cloud.
Realize Data Security
Since all the data is transmit using Internet, data security is of major concern in the cloud. Here are key contrivance for protecting data.
- Access Control
- Auditing
- Authentication
- Authorization
All of the service models should incorporate security contrivance operating in all above-mentioned areas.
secluded Access to Data
Since data stored in cloud can be accessed from everywere, we must have a contrivance to isolate data and protect it from client’s direct access.
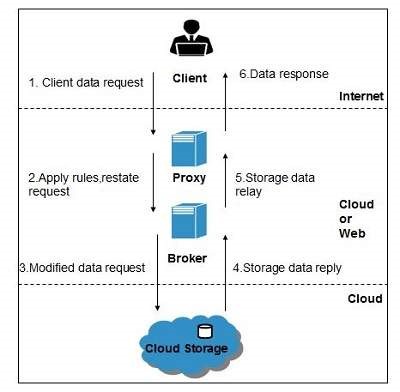
Brokered Cloud Storage Access is an approach for secluded storage in the cloud. In this approach couple of services are created:
- A broker with full eruption to storage but no access to client.
- A proxy with no eruption to storage but access to both client and broker.
Working Of Brokered Cloud Storage Access System
When the client issues demand to access data:
- The client data demand goes to the external service interface of proxy.
- The emissary forwards the request to the broker.
- The broker demand the data from cloud storage system.
- The cloud storage system go back the data to the broker.
- The brokers go back the data to proxy.
- Finally the attorney sends the data to the client.
All of the mentioned steps are shown in the following diagram:
Encryption
Encryption helps to guard data from being compromised. It guard data that is being transferred as well as data stored in the cloud. Even though encryption helps to protect data from any unauthorized access, it does not prevent data loss.